From Post-Mortem Monitoring to Real-Time Enforcement.
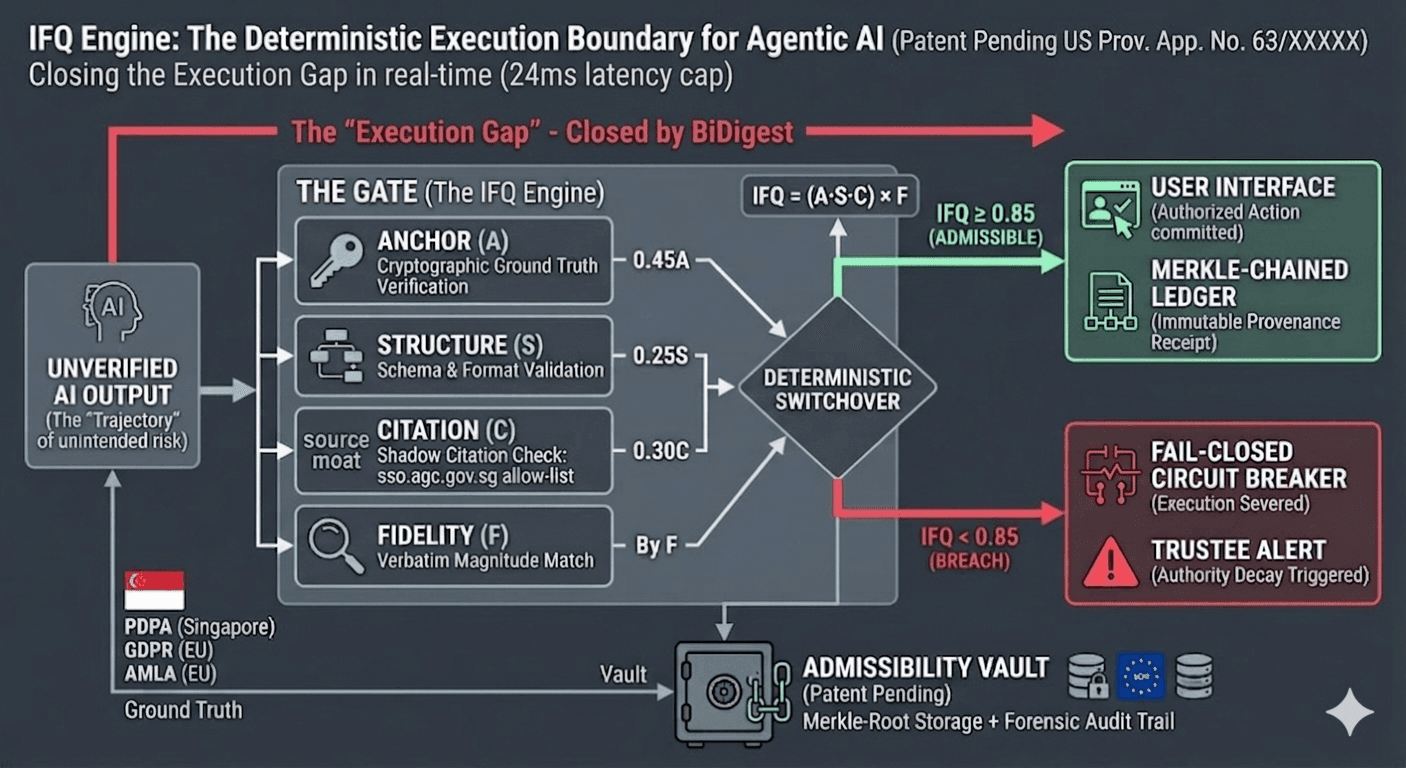
Traditional governance detects drift after the damage is done. BiDigest stops inadmissible AI actions at the execution boundary—before they become operational facts. The gate is deterministic and model-vendor independent: it does not outsource admissibility to an LLM’s probabilistic “safety” verdict.
Feature availability
- [SHIPPED]Integrity baselinePhase 3 — commit / bundle integrity on governed paths, evidenced by chained hashing and execute-boundary validation (independent of model vendor / inference path). See Phase 3 acceptance + archived report.
- [SPEC]SARD admissibilitySynchronous admissibility re-derivation at execute — spec / roadmap, not production for all routes.
- [DRAFT]SACI methodologyInternal State of AI Compliance Index framework; public dataset / index not implemented.
From intent to commit: T₀ and T₁
T₀ is when an action is first presented—routing, payload shape, and early gates treat it as unverified intent. T₁ is the commit boundary: deterministic checks run again before anything binding happens, including org lifecycle (active vs suspended). If the organization is inactive, API authentication returns HTTP 403; on seal paths, telemetry can be shunted with breach codes such as ORG_SUSPENDED_AT_T1 where applicable—fail-closed, not a “best effort” filter.
Wall-clock time is route- and deployment-dependent. Governed egress sealing and staleness monitoring use different cron paths—do not promise one universal sub-50ms wall on every integration.
Canonical definitions: Trustee handbook.
From discovery to resolution: the forensic anchor
Red-team partners catch drift; BiDigest adds a provider-agnostic boundary—Merkle-sealed lineage, npm run trustee:verify-batch-json so you can verify yourself, and HTTP that fails closed when something does not match—no quiet mismatch commits.
Persisted governance telemetry (SACI §9) ships with Phase A+B; today’s shipped posture is fail-closed responses plus ledger and receipt artifacts on trustee paths.
Shipped artifacts: Phase 3 report JSON, SECURITY.md, trustee verify CLIs.
Request methodology briefingThe Visibility Gap
Monitoring tools tell you what went wrong yesterday. By then, the regulatory breach is already on the ledger.
The execution gap
Drift accumulates between “looks fine in monitoring” and “commits as operational fact.” BiDigest re-validates authority at the commit boundary (T₁)—including org lifecycle—so inactive tenants can receive 403 at ingress and seal paths can record structured breach signals instead of quiet success.
The Admissibility Gap
Without Merkle-sealed proof, an AI action is legally indefensible. We provide the WORM-compliant evidence required for audit.
Not a Wrapper.
A Synchronous Intercept.
Wrappers and filters are suggestive — they sit outside the execution path. BiDigest performs a Structural Intercept on the wire. We don't trust the AI; we hold the commit.
"We don't try to make the AI safer. We make the infrastructure incapable of executing a breach."
The Execution Graph
Dual-boundary governance in one linear path—from Ground Truth upstream to the commit boundary downstream.
1. Lock the Standard
2. Catch the Intent
3. Enforce Consensus
4. Fail-Closed (No Committed Effect)
The IFQ Engine
We do not rely on probabilistic LLM "safety" prompts. Admissibility is a mathematical certainty. The Identity Fidelity Quotient (IFQ) is calculated at the execution boundary.
Patent pending — US Prov. App. No. 63/XXXXX
Translation for the Board
"If the AI uses the wrong source or violates a structural contract, the score drops to zero and the gate closes. No exceptions."
Identity (A — Anchor)
Matches the payload against hard tokens from your Ground Truth. We rely on statutory anchors, not paraphrased blog summaries, to drive what the gate may admit.
Structure (S — Schema)
Ensures requests and payloads satisfy structural contracts at the boundary. “Valid JSON” cannot be used to mask invalid regulatory obligations.
Citation & fidelity (C × F)
Enforces citation integrity. Shadow Sources (outdated or rogue URLs) must be on your allow-list. Fidelity (F) acts as the multiplier, mathematically tying the output tokens back to the anchored reference text. A “right answer” from the “wrong source” yields an IFQ of zero.
Merkle-Chained Forensics
This receipt is the only document that survives an SEC or Bank of England forensic audit. It proves the "Why" behind every "Yes" or "No".
Tamper-Proof Ledger
A SHA-256 hashed record of the exact AI payload and the Ground Truth anchor.
Audit Ready
Export the enforcement path for insurers, the SEC, or PRA supervisors.
{
"phase": "EXECUTE",
"ifq_score": 0.97,
"anchor_id": "GDPR-Art-32",
"merkle_root": "0xdef456...",
"status": "ADMITTED"
}
WORM COMPLIANT STORAGE
Ready to Hardent the Boundary?
Stop monitoring the damage. Start enforcing the standard. Deploy the BiDigest Control Plane in under 15 minutes.